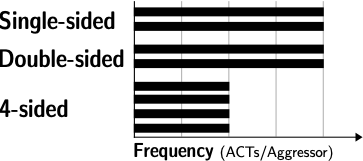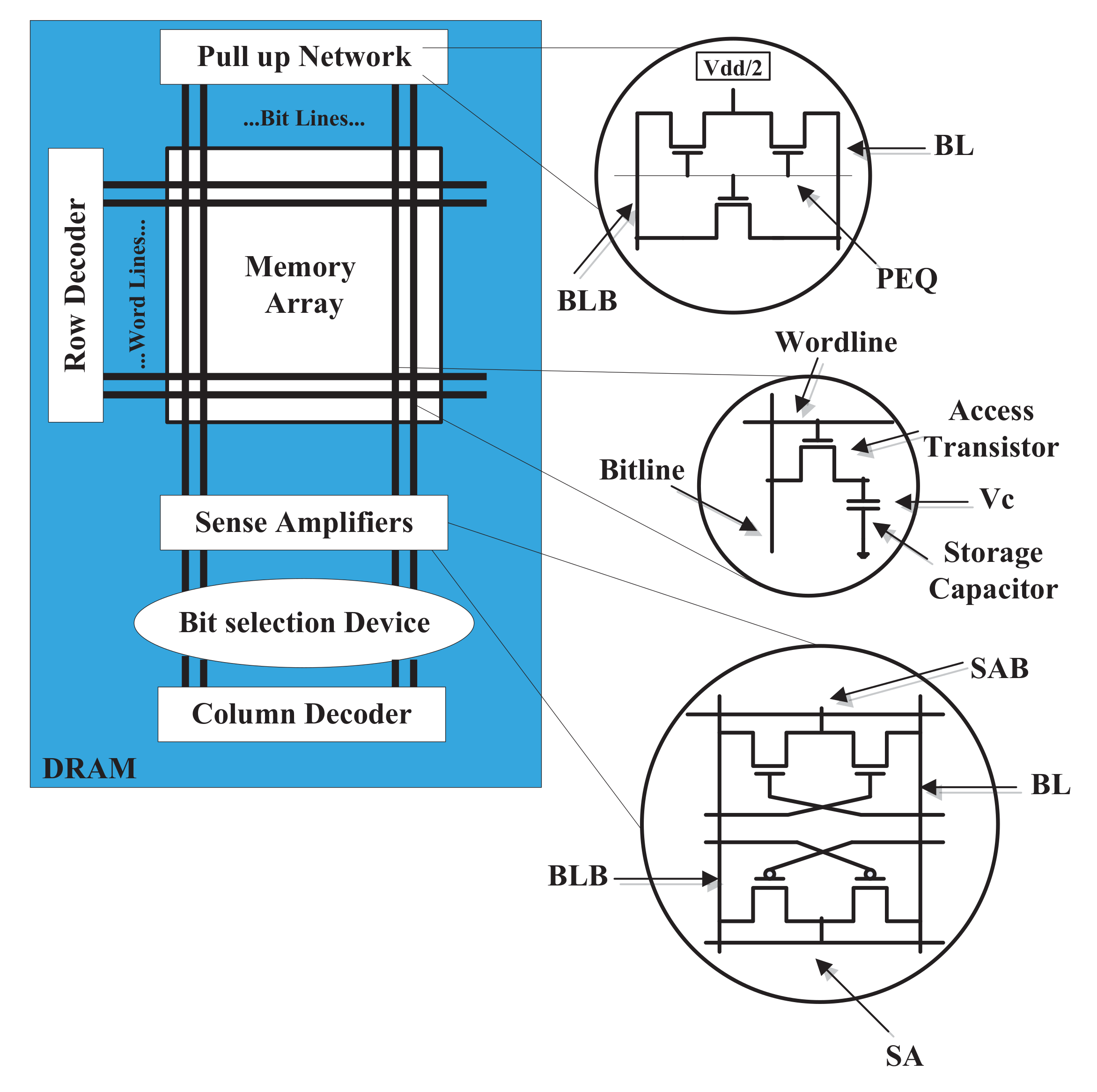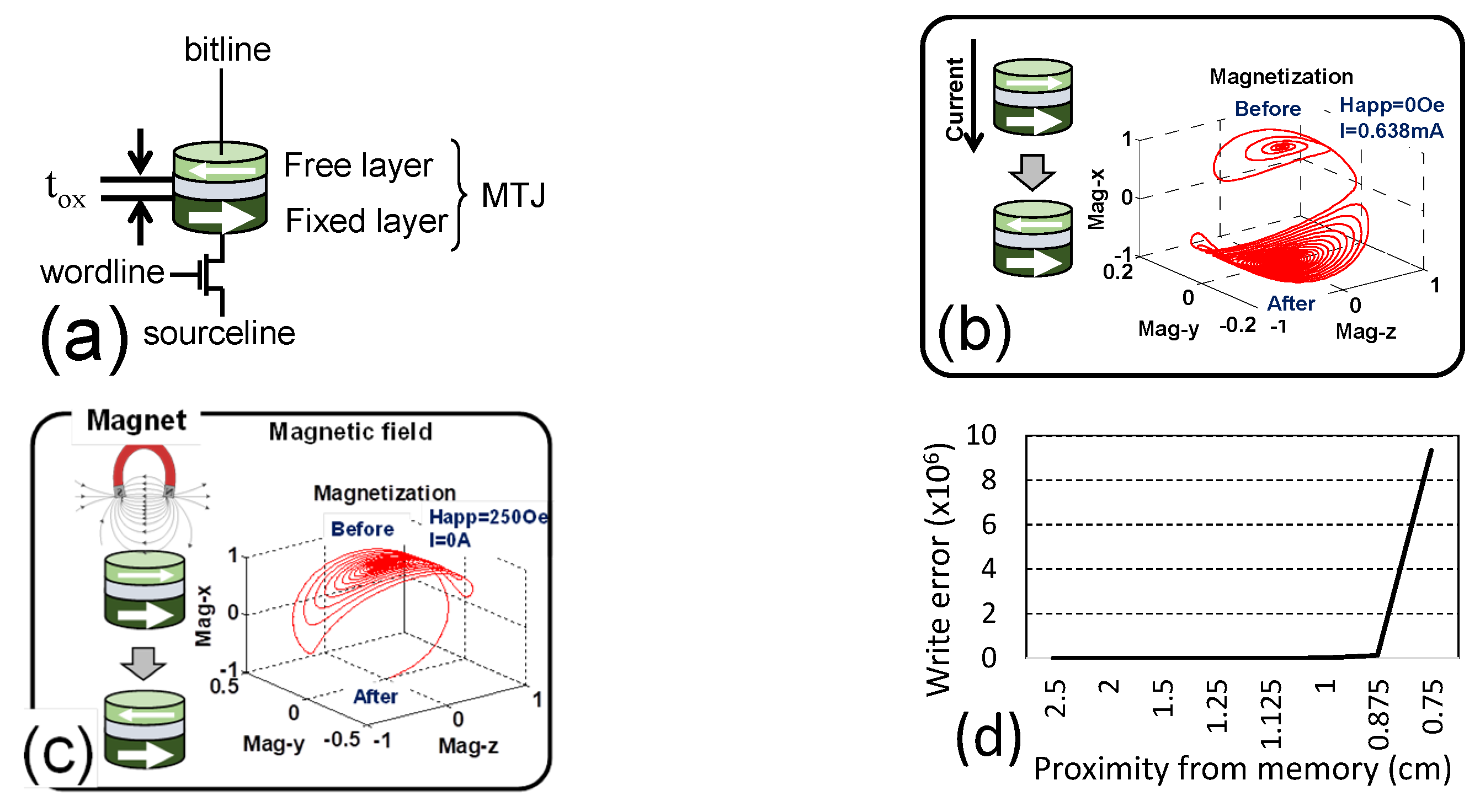
JLPEA | Free Full-Text | Comprehensive Study of Security and Privacy of Emerging Non-Volatile Memories

The Story of Rowhammer - Secure Hardware, Architectures, and Operating Systems Keynote - Onur Mutlu - YouTube
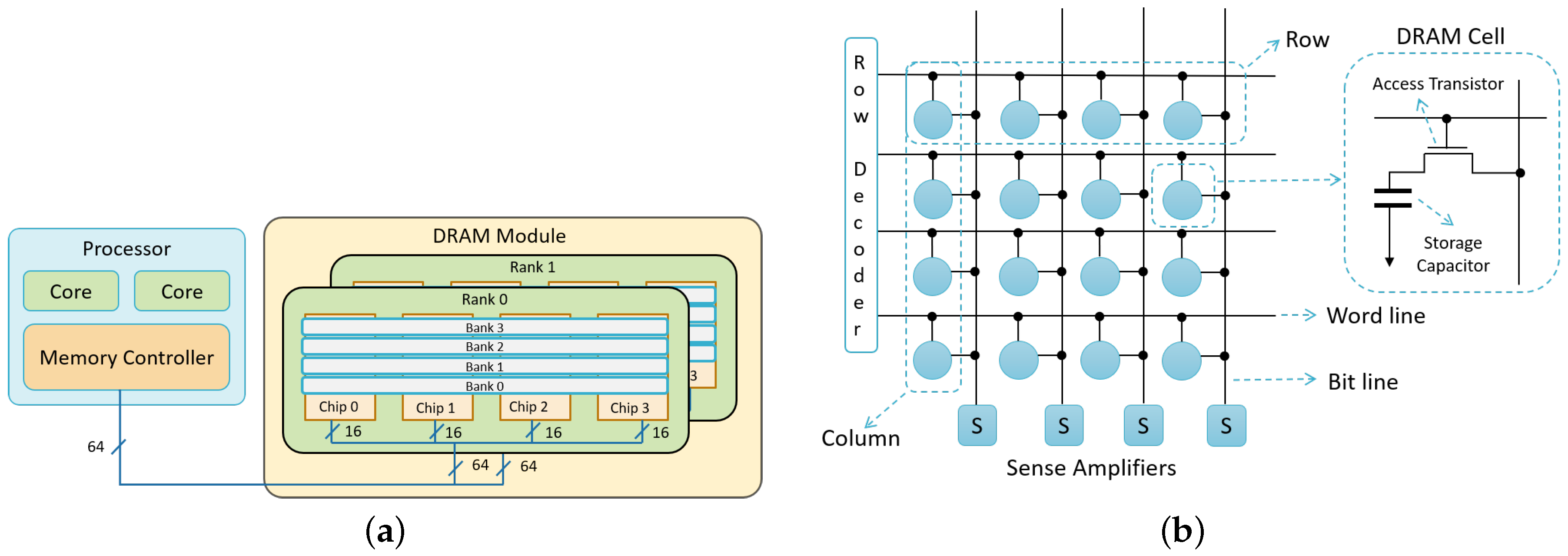
Applied Sciences | Free Full-Text | DRAM Retention Behavior with Accelerated Aging in Commercial Chips